Search N5 Net Software Repository:
Search Files
Sponsor:
Browse:
- Audio & Multimedia (1527)
- Business (1697)
- Communications (462)
- Desktop (135)
- Development (555)
- Education (163)
- Games & Entertainment (700)
- Graphic Apps (657)
- Home & Hobby (102)
- Network & Internet (524)
- Security & Privacy (499)
- Servers (65)
- System Utilities (8668)
- Web Development (279)
Areas Of Interest
Authors Area
Are you a software author? Take a look at our Author Resource Center where you will find marketing tools, software specifically created for promoting your software and a ton of other helpful resources.
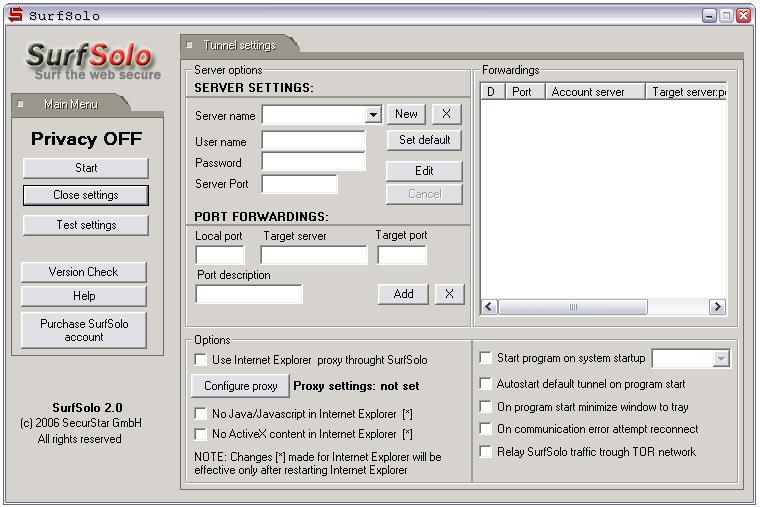
SurfSolo 2.0
No one knows more about ?surfing? and downloading habits than your ISP (Internet Service Provider). The ISP is able to know who you are, every site you visit, every page you view, and every file you download. How this happens? Every time you are connected on the Internet your ISP gives you an IP number that is a unique address which identifies you from the other computers on the network living you vunerable to any attacks from hackers or eavesdroppers. SurfSolo was created to protect you from those problems. Powerful software that allows the user to get totally anonymous and at the same time protects the data exchange on the Internet.The software provides a direct encrypted link(by using SSH Protocol) with one of the world wide SecurStar high bandwidth security proxy servers. ?SSH protocol (Secure Shell protocol)? which makes the connection encrypted from your personal computer to any website. A protocol says which format the data is going to be sent and which rules will be applied. The SSH protocol creates a ?virtual tunnel?, in such a way you are totally invisible from any kind of monitoring. If someone tries to track your IP number, it will recognize only our SecurStar server's IP, so it would be impossible to track your personal IP number. The SurfSolo also provides free e-mail account (no mailbox size limit). Sending emails from it will not reveal your personal IP number. At the moment SecurStar has 5 proxy servers available around the world (Malaysia, Hong Kong, Germany, Holland and Czech Republic).When the customer purchases the software he can choose one of the Proxy servers available.
Specifications:
Version: 2.0 |
Download
|
Similar Products:
Security & Privacy :: Other
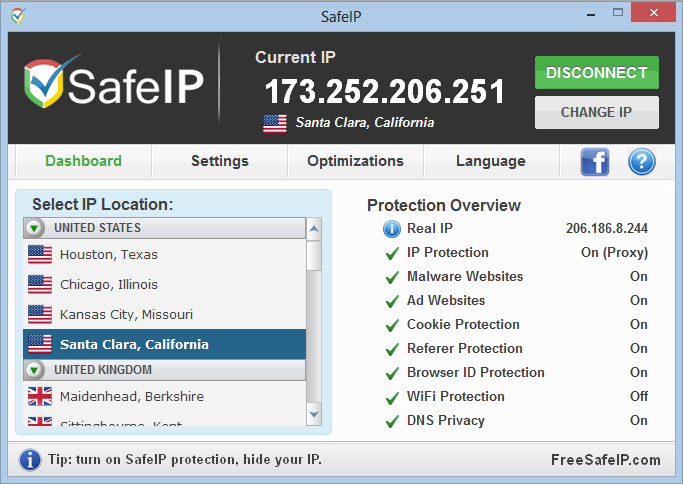 Surf anonymously, hide your IP address, and unblock websites, all for free with SafeIP. Select your preferred proxy IP location and change your IP address at anytime. The automatic startup option will ensure your IP is protected at all times, even before your Internet connection starts. Stop ads, cookies, and malware, while using our proprietary Browser Fingerprint anti-tracking technology. Application translations available in 24 languages.
Surf anonymously, hide your IP address, and unblock websites, all for free with SafeIP. Select your preferred proxy IP location and change your IP address at anytime. The automatic startup option will ensure your IP is protected at all times, even before your Internet connection starts. Stop ads, cookies, and malware, while using our proprietary Browser Fingerprint anti-tracking technology. Application translations available in 24 languages.
Windows | Freeware
Read More
Security & Privacy :: Other
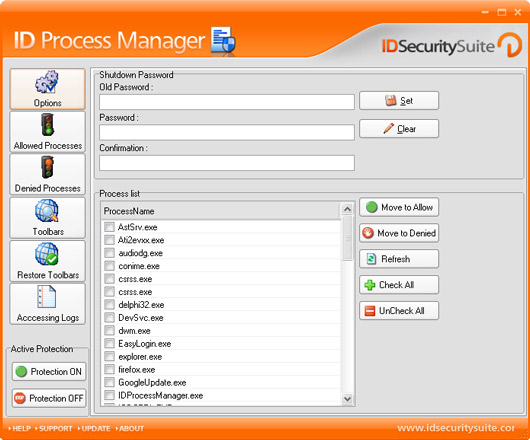 ID Process Manager is a program designed to help you manage the status of all processes on your computer. It enables you to stop any process or to start a new one, protecting against intruders, including spyware and Trojans. Main features includes: managing processes status, monitoring and removing of harmful processes, protecting against adware and Trojans, deleting and blocking of BHO, securing your shutdown process under password.
ID Process Manager is a program designed to help you manage the status of all processes on your computer. It enables you to stop any process or to start a new one, protecting against intruders, including spyware and Trojans. Main features includes: managing processes status, monitoring and removing of harmful processes, protecting against adware and Trojans, deleting and blocking of BHO, securing your shutdown process under password.
Windows | Shareware
Read More
Security & Privacy :: Other
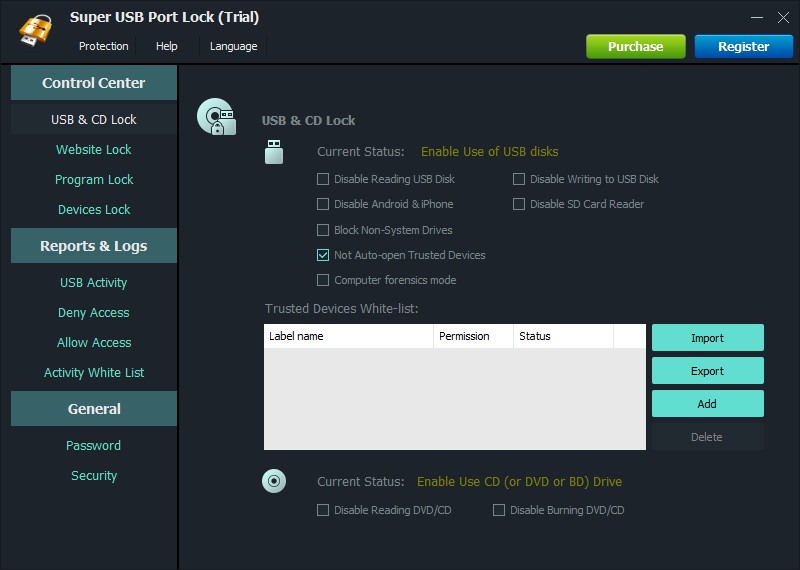 Super USB Port Lock prevents data leaks through devices like USB drives, phones, tablets and other devices that are attached to your computer. It also prevents data leaks through any websites and programs.
Super USB Port Lock prevents data leaks through devices like USB drives, phones, tablets and other devices that are attached to your computer. It also prevents data leaks through any websites and programs.
Windows | Shareware
Read More
Security & Privacy :: Other
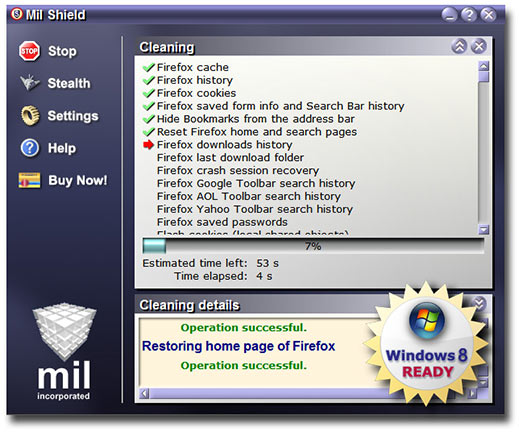 Mil Shield protects your privacy by deleting all tracks from your online or offline PC activities: Cookies, Cache, History, WebCacheV01.dat and INDEX.DAT files, Registry, Free Disk Space, and many others. Some unique options in this program: Selective cleaning (selectively preserves cache, history and cookies for chosen by you safe Internet sites), Panic key combination,Automatic cleaning. Supports Win 8.1/7/Vista/XP 32&64-bit, IE 11, Chrome.
Mil Shield protects your privacy by deleting all tracks from your online or offline PC activities: Cookies, Cache, History, WebCacheV01.dat and INDEX.DAT files, Registry, Free Disk Space, and many others. Some unique options in this program: Selective cleaning (selectively preserves cache, history and cookies for chosen by you safe Internet sites), Panic key combination,Automatic cleaning. Supports Win 8.1/7/Vista/XP 32&64-bit, IE 11, Chrome.
Windows | Shareware
Read More