Search N5 Net Software Repository:
Search Files
Sponsor:
Browse:
- Audio & Multimedia (1527)
- Business (1697)
- Communications (462)
- Desktop (135)
- Development (555)
- Education (163)
- Games & Entertainment (700)
- Graphic Apps (657)
- Home & Hobby (102)
- Network & Internet (524)
- Security & Privacy (499)
- Servers (65)
- System Utilities (8668)
- Web Development (279)
Areas Of Interest
Authors Area
Are you a software author? Take a look at our Author Resource Center where you will find marketing tools, software specifically created for promoting your software and a ton of other helpful resources.
Power Spy Lite 2.110
Security & Privacy :: Covert Surveillance
Power Spy Lite Software lets you know exactly what people do on a computer while you are away. It secretly logs Facebook, keystrokes, chats & IMs, emails, websites visited, photos shared, videos watched, video talk, user names, passwords, applications run, internet searches and much more. It takes screenshots every x seconds like a surveillance camera pointing at the monitored PC, which records Facebook and other Windows store apps like WhatsApp, Messenger, Telegram, Viber, etc. The spy software starts monitoring with system startup then runs silently and invisibly. Only administrator of the software can bring it back with hotkey and manage it. It automatically sends log reports to your specified email or ftp, like every 30 minutes. You can check these reports on another remote PC, tablet or even a smart phone. You can also view logs directly from its control panel on the monitored PC. Power Spy Lite is perfect for catching cheaters, monitoring employees, children and spouse, protecting kids online, collecting evidence and even investigating crimes. It is loved by many parents, employers, doctors and teachers. In the past ten years, it has helped thousands of parents protect their kids online from child molesters, drug dealers and malicious websites, and it has been installed on thousands of office computers to maintain employee discipline.
Specifications:
Version: 2.110 |
Download
|
Similar Products:
Security & Privacy :: Covert Surveillance
 Lock the Bad Guys out of your USB ports with MyUSBOnly; Block Untrusted USB Memory Stick Activity in Office. Prevent data theft by blocking all but your trusted USB storage devices. Stop your files from walking away on thumb drives, mp3 players, flash cards and portable USB hard drives. Secretly log all USB connect, disconnect and files/folders copied, modified, deleted activity. This version is not time-limited!
Lock the Bad Guys out of your USB ports with MyUSBOnly; Block Untrusted USB Memory Stick Activity in Office. Prevent data theft by blocking all but your trusted USB storage devices. Stop your files from walking away on thumb drives, mp3 players, flash cards and portable USB hard drives. Secretly log all USB connect, disconnect and files/folders copied, modified, deleted activity. This version is not time-limited!
Windows | Freeware
Read More
Security & Privacy :: Covert Surveillance
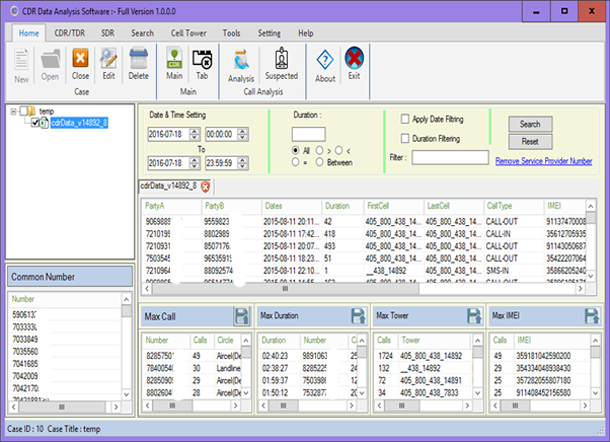 ATS Call Data Record analyzer can import and analyze CDR/Tower CDR Data from any service provider in India or Other Country and Its generates a comprehensive report of frequency statistics including service provider details and subscriber details.
ATS Call Data Record analyzer can import and analyze CDR/Tower CDR Data from any service provider in India or Other Country and Its generates a comprehensive report of frequency statistics including service provider details and subscriber details.
Windows | Shareware
Read More
CLASSROOM SPY PROFESSIONAL 5.6.4
Security & Privacy :: Covert Surveillance
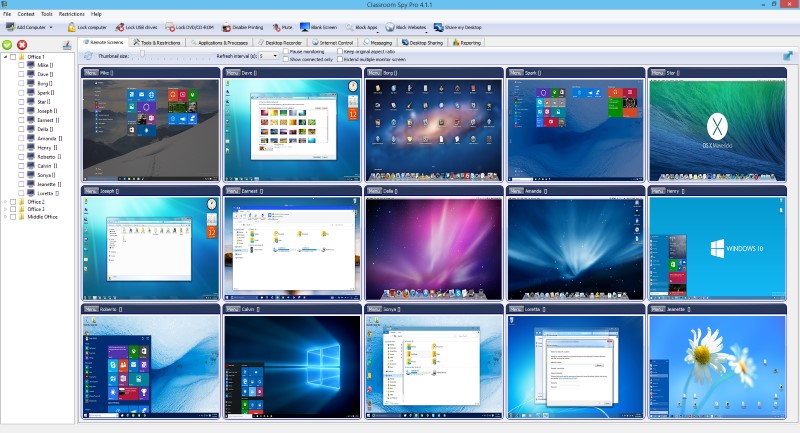 A simple and powerful classroom management software that allows you to see live screens of student computers or show you screen to students. You can take control of a remote computer by controlling the mouse and keyboard. Additionally you can also record student's screens. Several tools allow you to turn off, restart, hibernate.... remote computers with one click. Starting program on remote computers is easy.
A simple and powerful classroom management software that allows you to see live screens of student computers or show you screen to students. You can take control of a remote computer by controlling the mouse and keyboard. Additionally you can also record student's screens. Several tools allow you to turn off, restart, hibernate.... remote computers with one click. Starting program on remote computers is easy.
Windows | Shareware
Read More
NET MONITOR FOR EMPLOYEES PROFESSIONAL 6.6.4
Security & Privacy :: Covert Surveillance
 This employee monitoring software allows you to see live screens of remote computers or show you screen to employees. You can take control of a remote computer by controlling the mouse and keyboard. This way, you can always watch what users are doing on the remote computer. Additionally you can also record employee screens. With this activity monitoring software you can turn off, restart, hibernate.... remote computers with one click.
This employee monitoring software allows you to see live screens of remote computers or show you screen to employees. You can take control of a remote computer by controlling the mouse and keyboard. This way, you can always watch what users are doing on the remote computer. Additionally you can also record employee screens. With this activity monitoring software you can turn off, restart, hibernate.... remote computers with one click.
Windows | Shareware
Read More