Search N5 Net Software Repository:
Search Files
Sponsor:
Browse:
- Audio & Multimedia (1572)
- Business (1734)
- Communications (470)
- Desktop (180)
- Development (572)
- Education (166)
- Games & Entertainment (708)
- Graphic Apps (684)
- Home & Hobby (105)
- Network & Internet (542)
- Security & Privacy (505)
- Servers (65)
- System Utilities (9409)
- Web Development (284)
Areas Of Interest
Authors Area
Are you a software author? Take a look at our Author Resource Center where you will find marketing tools, software specifically created for promoting your software and a ton of other helpful resources.
Digital Security Suite 2011
Get Digital Security Suite. This package contains both the Digital Document Shredder and the Digital Document Encryptor in one complete suite. Windows 7, Vista and XP certified and awarded software suitable for both the enterprise and private user. Encrypt sensitive documents and other private digital information you have on your computer. Product reknowned for it's user-friendliness. Supports up to 480 bit strong encryption. Ideal for encrypting attachements to be sent by email. The software also allows you to permanently remove selected information on your hard drive and other memories. When you delete a file, empty your Recycle Bin or even format your hard disk, the information is NOT removed from your computer. These commands only alter the structure of the drive, leaving most of the data intact and recoverable with software tools easily available. This means that someone else can recreate the files that you think you have already deleted. The only true way to permanently remove unwanted files and data is to use file shredding software. File shredding utilizes an advanced algorithm technique of overwriting your files multiple times so that the information contained in them is no longer readable, thus destroying the original data forever. The following standards and technologies are currently supported: AES-standard Rijndael, 256 bits Blowfish, 448 bits Twofish, 256 bits SafeIT-algorithm, 480 bits Hash-algorithm: MD5 HMG Infosec Standard 5, Baseline & Enhanced Peter Gutmann's algorithm U.S.Department of Defense Sanitizing (DOD 5220.22-M) Bruce Schneier's algorithm. Navy Staff Office Publication (NAVSO P-5239-26) for RLL The National Computer Security Center (NCSC-TG-025) Air Force System Security Instruction 5020 US Army AR380-19 German Standard VSITROPNAVINST 5239.1A
Specifications:
Version: 2011 |
Download
|
Similar Products:
BATCH FILE MANAGER FREE 5.0.135
System Utilities :: File & Disk Management
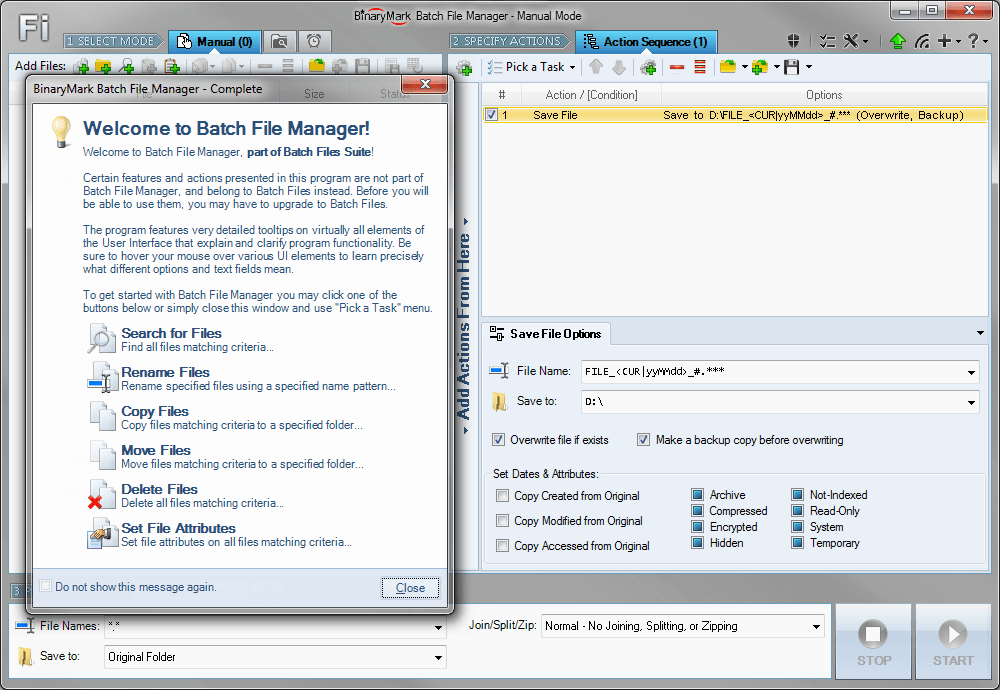 Rename, move, copy, delete, and otherwise manage multiple files. Rename multiple files according to the rules and pattern you specify using powerful editor with syntax highlighting. Copy and move files to folders specified using absolute/relative paths. Select files for processing based on their name, dates, size, text/binary contents using advanced file search supporting RegEx and advanced wildcards. Delete files easily.
Rename, move, copy, delete, and otherwise manage multiple files. Rename multiple files according to the rules and pattern you specify using powerful editor with syntax highlighting. Copy and move files to folders specified using absolute/relative paths. Select files for processing based on their name, dates, size, text/binary contents using advanced file search supporting RegEx and advanced wildcards. Delete files easily.
Windows | Shareware
Read More
System Utilities :: Automation Tools
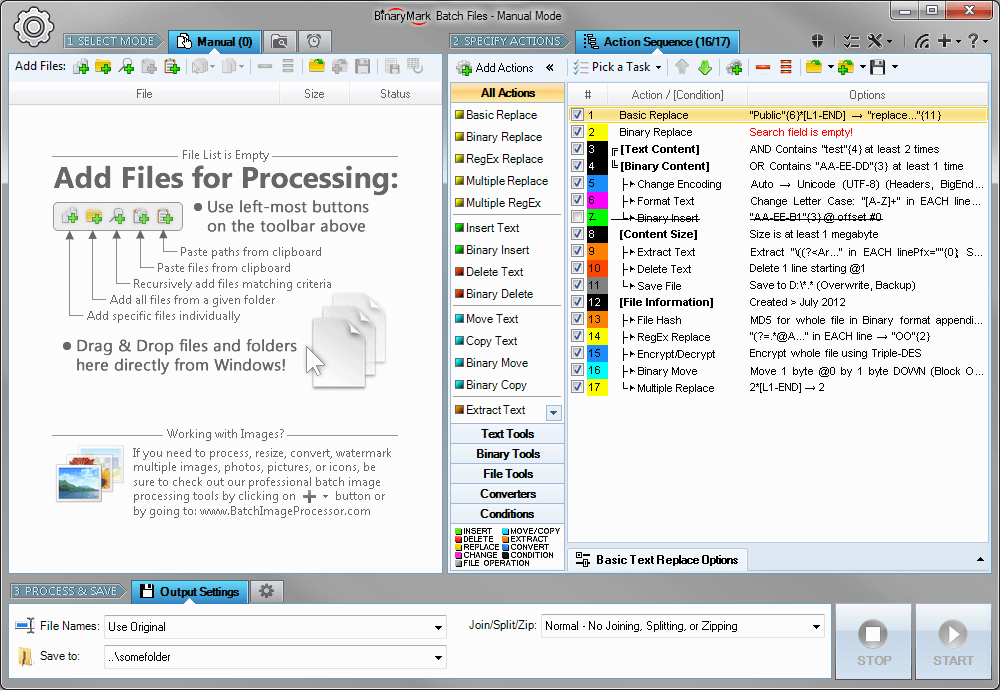 Replace, insert, delete, copy, move, format, extract, convert, encode, encrypt text and bytes in multiple files. Process 1000s files using multiple CPU cores in manual, automatic/continuous, triggered/scheduled, or console modes, or directly from Windows Explorer right-click menu. Save files with original or new name defined by a mask. Select files for processing based on their name, dates, size, and contents using advanced file search.
Replace, insert, delete, copy, move, format, extract, convert, encode, encrypt text and bytes in multiple files. Process 1000s files using multiple CPU cores in manual, automatic/continuous, triggered/scheduled, or console modes, or directly from Windows Explorer right-click menu. Save files with original or new name defined by a mask. Select files for processing based on their name, dates, size, and contents using advanced file search.
Windows | Shareware
Read More
CUBEXSOFT OUTLOOK DUPLICATE REMOVER 1.1
System Utilities :: File & Disk Management
 Need to know how to delete Outlook duplicate mailbox, then go with the CubexSoft Outlook Duplicate Remover Tool ? a best and automated tool to perfectly and precisely remove all duplicate items from Outlook along with all emails, and attachments. The Outlook Duplicate Remover tool also allows selective duplicate deletion from Outlook mailbox with help of date-filter facility.
Need to know how to delete Outlook duplicate mailbox, then go with the CubexSoft Outlook Duplicate Remover Tool ? a best and automated tool to perfectly and precisely remove all duplicate items from Outlook along with all emails, and attachments. The Outlook Duplicate Remover tool also allows selective duplicate deletion from Outlook mailbox with help of date-filter facility.
Windows | Shareware
Read More
System Utilities :: File & Disk Management
 Secure Eraser uses the most renowned method of data disposal and overwrites sensitive information in such a reliable way that it can never be retrieved even with specialized software. Our multiple award-winning solutions for definitively destroying data also eliminate any cross-references that could leave traces of deleted files in the allocation table of your hard drive.
Secure Eraser uses the most renowned method of data disposal and overwrites sensitive information in such a reliable way that it can never be retrieved even with specialized software. Our multiple award-winning solutions for definitively destroying data also eliminate any cross-references that could leave traces of deleted files in the allocation table of your hard drive.
Windows | Freeware
Read More