Search N5 Net Software Repository:
Search Files
Sponsor:
Browse:
- Audio & Multimedia (1582)
- Business (1741)
- Communications (469)
- Desktop (134)
- Development (571)
- Education (165)
- Games & Entertainment (709)
- Graphic Apps (683)
- Home & Hobby (106)
- Network & Internet (544)
- Security & Privacy (505)
- Servers (67)
- System Utilities (9267)
- Web Development (284)
Areas Of Interest
Authors Area
Are you a software author? Take a look at our Author Resource Center where you will find marketing tools, software specifically created for promoting your software and a ton of other helpful resources.
CryptIt 1.4
Security & Privacy :: Encryption Tools
Most file encryptors use methods that rely on the theory of computational security, that is the difficulty of key factorisation prevents decryption ofthe file. But this method may not work forever. It used to be considered that a 56 bit key was unbreakable to brute force attacks, but the government of the USA now requires all Top Secret data to use keys of at least 192 bits. This bar will keep raising as computing power increases. (It is argued by some though that this will never happen due to the laws of physics!) CryptIt is designed to use conventional XOR encryption on keys that are the same size as the file to be encrypted. Furthermore, if you use an unpredictable file that is the same size (or larger) than the original file and you use this file only once, this is known as a one-time pad and it is completely unbreakable, even to computers 1000 years from now. This is because there is no algorithm at all, just a big key, and thus there is no pattern to follow once you have decrypted any part of the file. Thus attempts to decrypt it could result in any file, and there would be no way to verify that it has decrypted correctly. CryptIt can also has some convenience features such as being able to automatically use pad files generated by our program GigAlarm, generate key files (from a stream cipher and thus not best for OTP usage) and also analyse the suitability of your chosen key file. CryptIt also has a ability to use removable media (USB drives, CDs, floppies) as a key code book, further increasing the security and convenience of the method. If your needs are more simpler then you can also use a word (string), but the advantages of the XOR method are lost then. Descriptions can be stored within the encrypted file, as well as the file name of the code. Command line operation is also supported and CryptIt is written in Assembly Language for maximum efficiency.
Specifications:
Version: 1.4 |
Download
|
Similar Products:
BATCH FILE ENCRYPT FREE 5.0.135
Security & Privacy :: Encryption Tools
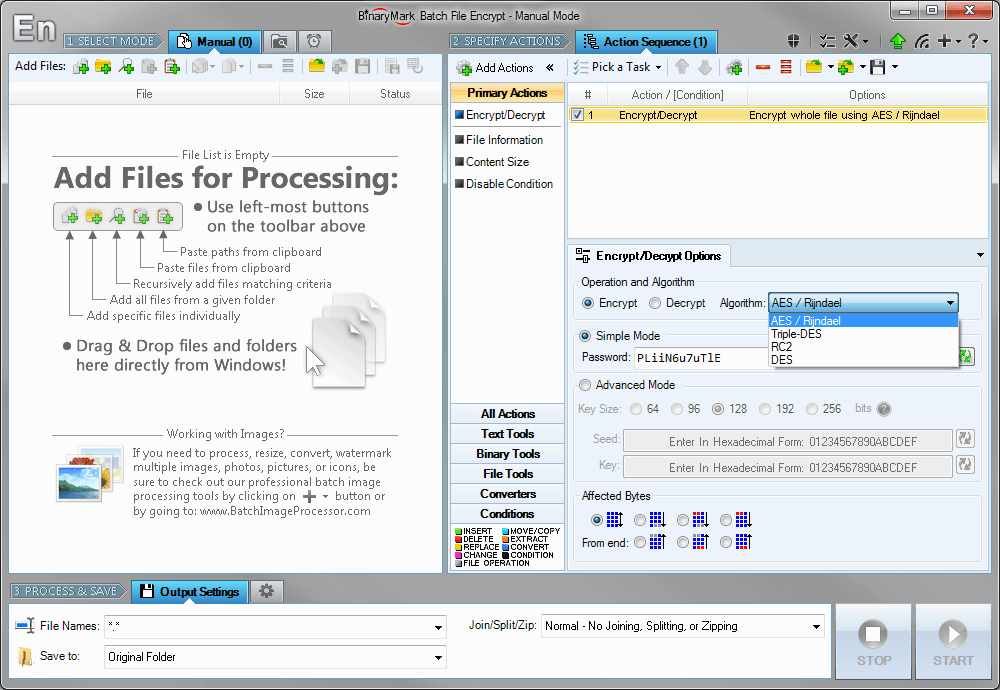 Encrypt and decrypt whole files or their parts using AES, Triple-DES (3DES), RC2, and DES symmetric algorithms. You can encrypt files with a single password or specify cryptographic keys (vectors) instead. You can change key bit length for better protection. You can select specifically which bytes in a file should be encrypted/decrypted, though by default the whole file is processed.
Encrypt and decrypt whole files or their parts using AES, Triple-DES (3DES), RC2, and DES symmetric algorithms. You can encrypt files with a single password or specify cryptographic keys (vectors) instead. You can change key bit length for better protection. You can select specifically which bytes in a file should be encrypted/decrypted, though by default the whole file is processed.
Windows | Shareware
Read More
Audio & Multimedia :: CD Burners
 PowerISO is a powerful CD/DVD/BD image file processing tool, which allows you to open, extract, create, edit, compress, encrypt, split and convert ISO files, and mount these files with internal virtual drive. It can process almost all CD/DVD/BD image files including ISO and BIN. PowerISO can be used easily, which support shell integration, context menu, drag and drop, clipboard copy paste.
PowerISO is a powerful CD/DVD/BD image file processing tool, which allows you to open, extract, create, edit, compress, encrypt, split and convert ISO files, and mount these files with internal virtual drive. It can process almost all CD/DVD/BD image files including ISO and BIN. PowerISO can be used easily, which support shell integration, context menu, drag and drop, clipboard copy paste.
Windows | Shareware
Read More
Audio & Multimedia :: CD Burners
 PowerISO is a powerful CD/DVD/BD image file processing tool, which allows you to open, extract, create, edit, compress, encrypt, split and convert ISO files, and mount these files with internal virtual drive. It can process almost all CD/DVD/BD image files including ISO and BIN. PowerISO can be used easily, which support shell integration, context menu, drag and drop, clipboard copy paste.
PowerISO is a powerful CD/DVD/BD image file processing tool, which allows you to open, extract, create, edit, compress, encrypt, split and convert ISO files, and mount these files with internal virtual drive. It can process almost all CD/DVD/BD image files including ISO and BIN. PowerISO can be used easily, which support shell integration, context menu, drag and drop, clipboard copy paste.
Windows | Shareware
Read More
ARMORTOOLS PROFESSIONAL 26.2.1
Security & Privacy :: Encryption Tools
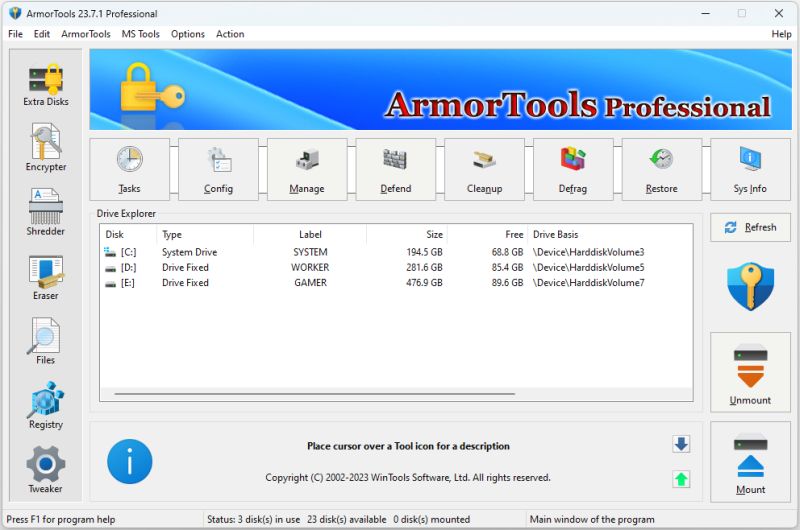 ArmorTools Professional is a set of tools that expands the capabilities of the MS Windows operating system in the field of security and protection of user confidential information. ArmorTools allows you to create secure virtual disks encrypted using AES128/AES256 algorithms, encrypt files and folder contents using any file as a password. ArmorTools removes traces of the user's work on the computer, clears the history of visiting sites...
ArmorTools Professional is a set of tools that expands the capabilities of the MS Windows operating system in the field of security and protection of user confidential information. ArmorTools allows you to create secure virtual disks encrypted using AES128/AES256 algorithms, encrypt files and folder contents using any file as a password. ArmorTools removes traces of the user's work on the computer, clears the history of visiting sites...
Windows | Shareware
Read More