Search N5 Net Software Repository:
Search Files
Sponsor:
Browse:
- Audio & Multimedia (1527)
- Business (1697)
- Communications (462)
- Desktop (135)
- Development (555)
- Education (163)
- Games & Entertainment (700)
- Graphic Apps (657)
- Home & Hobby (102)
- Network & Internet (524)
- Security & Privacy (499)
- Servers (65)
- System Utilities (8668)
- Web Development (279)
Areas Of Interest
Authors Area
Are you a software author? Take a look at our Author Resource Center where you will find marketing tools, software specifically created for promoting your software and a ton of other helpful resources.
Search: to do list software for windows
System Utilities :: File & Disk Management
 By using SQL recovery tool users speedily fix SQL database error and recover corrupt SQL server database. SQL database restore process involves recovery of MDF elements such as tables, views, queries, stored procedures etc. SQL Database Recovery Tool can be used to solve the query how I can restore SQL database in an efficient manner.
By using SQL recovery tool users speedily fix SQL database error and recover corrupt SQL server database. SQL database restore process involves recovery of MDF elements such as tables, views, queries, stored procedures etc. SQL Database Recovery Tool can be used to solve the query how I can restore SQL database in an efficient manner.
Windows | Shareware
Read More | Download Now
SQL SERVER BACKUP RESTORE SOFTWARE 5.0
System Utilities :: File & Disk Management
 SQL Server Backup Recovery Tool can easily restore corrupt SQL backup files and repair corrupt SQL backup files in an efficient manner. SQL Server backup recovery software easily restore corrupt SQL backup and repair entire database in fraction of minutes as software working functionality works very well and is a very viable solution in most environments. https://www.sqlrepairtool.org/sql-server-backup-restore-software.html
SQL Server Backup Recovery Tool can easily restore corrupt SQL backup files and repair corrupt SQL backup files in an efficient manner. SQL Server backup recovery software easily restore corrupt SQL backup and repair entire database in fraction of minutes as software working functionality works very well and is a very viable solution in most environments. https://www.sqlrepairtool.org/sql-server-backup-restore-software.html
Windows | Shareware
Read More | Download Now
SQLITE DATA RECOVERY TOOL 22.0
System Utilities :: File & Disk Management
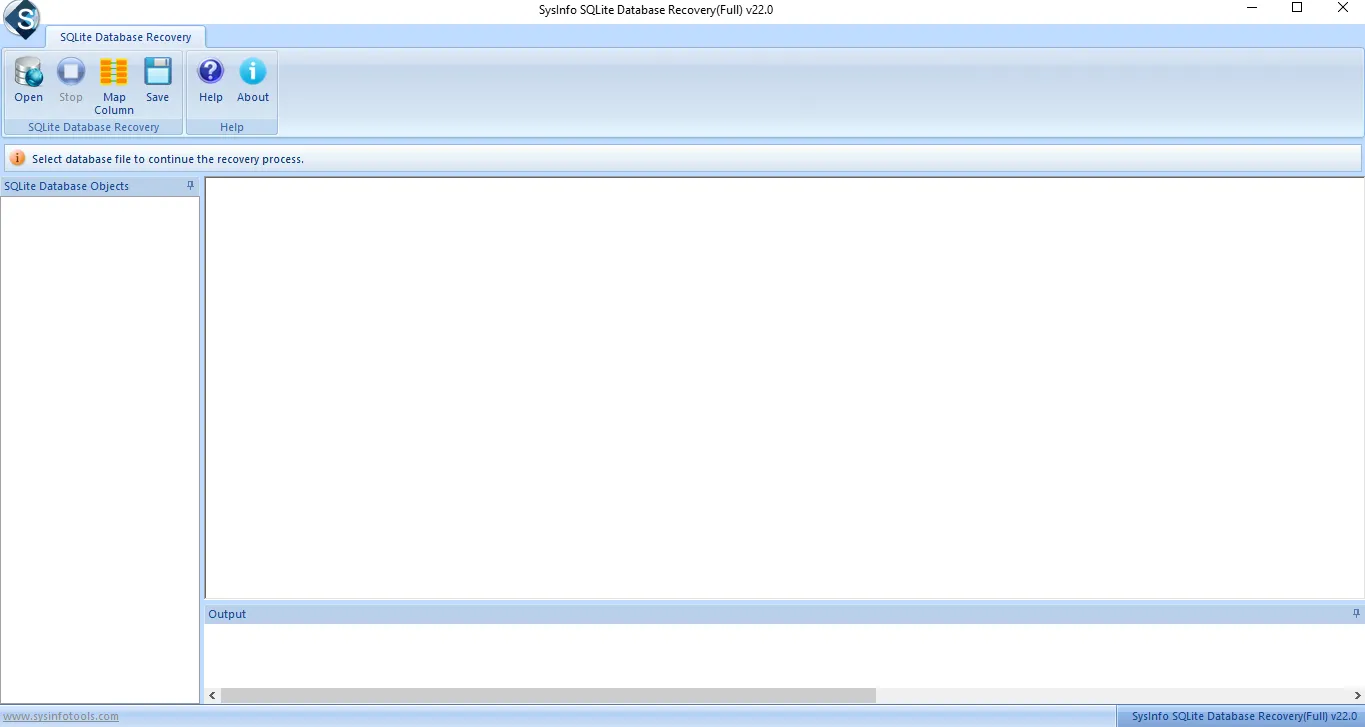 SQLite repair tool is developed with advanced and smart algorithms. One can easily fix corrupt SQLite Database with great ease. Also enables its users to recover various Database Objects like Tables, Indexes, Views, Triggers, etc . The tool saves the SQLite to MDB File safely and reliably. The SQLite database recovery serves its users with various amazing features like it also works for UTF - 8 & UTF - 16 SQLite data formats.
SQLite repair tool is developed with advanced and smart algorithms. One can easily fix corrupt SQLite Database with great ease. Also enables its users to recover various Database Objects like Tables, Indexes, Views, Triggers, etc . The tool saves the SQLite to MDB File safely and reliably. The SQLite database recovery serves its users with various amazing features like it also works for UTF - 8 & UTF - 16 SQLite data formats.
Windows | Shareware
Read More | Download Now
SQLITE DATABASE RECOVERY TOOL 22.0
System Utilities :: Backup & Restore
 SQLite Database Recovery Software is smartly developed with exciting features that help users to repair or fix SQLite Database corruption smoothly. Afterward, It restores SQLite database objects like Tables, triggers, views, indices, etc. It does not require any technical knowledge as it is designed with an interactive GUI, which helps users install and run the software smoothly. Every step is described in an easy way for users.
SQLite Database Recovery Software is smartly developed with exciting features that help users to repair or fix SQLite Database corruption smoothly. Afterward, It restores SQLite database objects like Tables, triggers, views, indices, etc. It does not require any technical knowledge as it is designed with an interactive GUI, which helps users install and run the software smoothly. Every step is described in an easy way for users.
Windows | Shareware
Read More | Download Now
SQLITE DATABASE REPAIR TOOL 18.0
System Utilities :: File & Disk Management
 SQLite Database Repair is a well-known tool that allows the repair of a corrupt SQLite database for multiple reasons. The SQLite Repair tool can successfully repair SQLite database objects such as tables, indices, triggers, views, etc. Whatever the issue arises, you can recover the SQLite database from corrupt .sqlite, .db, and.sqlite3 files and store them in a new SQLite or MDB file. It is intended for both technical and non-technical users.
SQLite Database Repair is a well-known tool that allows the repair of a corrupt SQLite database for multiple reasons. The SQLite Repair tool can successfully repair SQLite database objects such as tables, indices, triggers, views, etc. Whatever the issue arises, you can recover the SQLite database from corrupt .sqlite, .db, and.sqlite3 files and store them in a new SQLite or MDB file. It is intended for both technical and non-technical users.
Windows | Shareware
Read More | Download Now
System Utilities :: File & Disk Management
 Get this proficient SQLite db repair tool and repair damage SQLite database in few clicks. You can repair all corrupt SQLite db file data such as tables, views, fields, indexes, triggers, unique key, primary etc and can restore in MDB, MDF and .DB file format without any data loss. You can recover iphone address book contacts and recover browser history by using this tool.
Get this proficient SQLite db repair tool and repair damage SQLite database in few clicks. You can repair all corrupt SQLite db file data such as tables, views, fields, indexes, triggers, unique key, primary etc and can restore in MDB, MDF and .DB file format without any data loss. You can recover iphone address book contacts and recover browser history by using this tool.
Windows MAC Linux | Shareware
Read More | Download Now
Web Development :: ASP & PHP
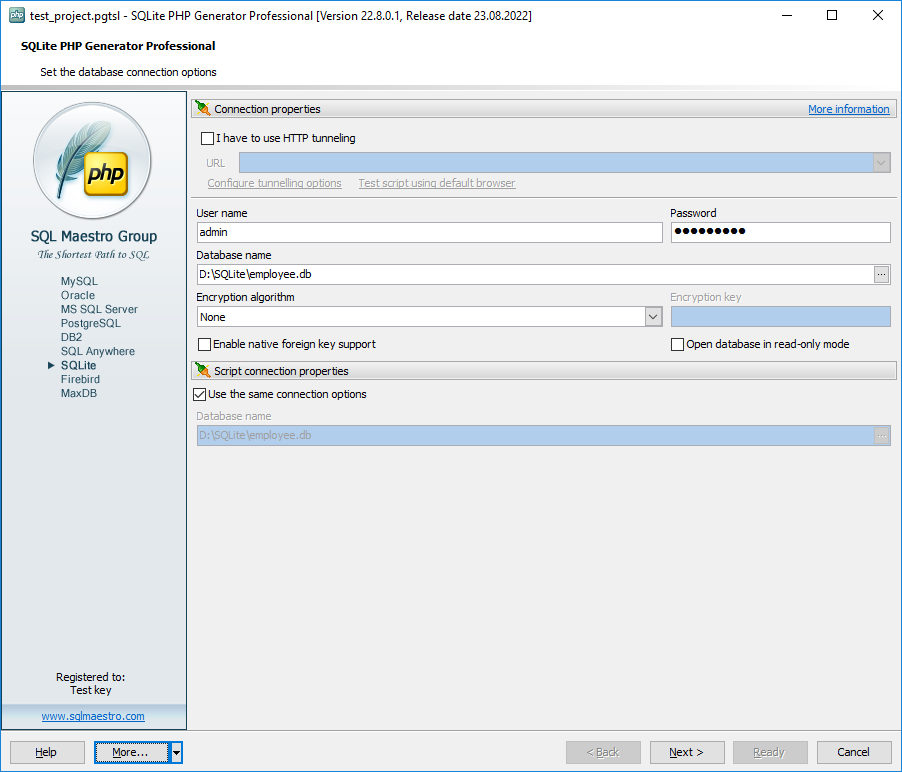 SQLite PHP Generator is a freeware but powerful SQLite GUI frontend that allows you to generate high-quality SQLite PHP scripts for the selected tables, views and queries for the further working with these objects through the web. With SQLite PHP Generator you will have a very professional web database application ready for uploading to your website.
SQLite PHP Generator is a freeware but powerful SQLite GUI frontend that allows you to generate high-quality SQLite PHP scripts for the selected tables, views and queries for the further working with these objects through the web. With SQLite PHP Generator you will have a very professional web database application ready for uploading to your website.
Windows | Freeware
Read More | Download Now
Business :: Databases & Tools
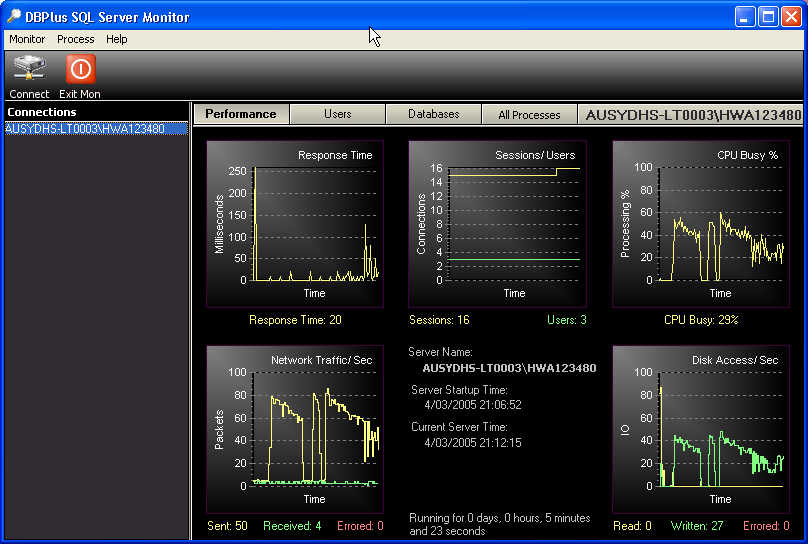 DBMonitor maintains and monitors Microsoft SQL Server database servers.
Alerts can be sent out when database servers disconnect unexpectly or there is a high usage on the server.
DBMonitor maintains and monitors Microsoft SQL Server database servers.
Alerts can be sent out when database servers disconnect unexpectly or there is a high usage on the server.
Windows | Shareware
Read More | Download Now
STAMP FREE ID3 TAG EDITOR 2.40
Audio & Multimedia :: Multimedia Creation Tools
 Stamp Free ID3 Tag Editor allows you to add or change the internal file information associated with an audio file. Software applications such as WavePad Audio Editor and portable music devices such as IPods read and display ID3 tag information and allow you to organize your music by, among other things, genre, artist and year.
Stamp Free ID3 Tag Editor allows you to add or change the internal file information associated with an audio file. Software applications such as WavePad Audio Editor and portable music devices such as IPods read and display ID3 tag information and allow you to organize your music by, among other things, genre, artist and year.
Windows | Freeware
Read More | Download Now
Audio & Multimedia :: Multimedia Creation Tools
 Stamp ID3 tag editor allows you to edit or add file information such as genre, title, artist, album, year, track number to audio files like .mp3's, .wav's and .ogg's. Just add the files you want to edit to the list, enter the new information, and then click the stamp button.
Stamp ID3 tag editor allows you to edit or add file information such as genre, title, artist, album, year, track number to audio files like .mp3's, .wav's and .ogg's. Just add the files you want to edit to the list, enter the new information, and then click the stamp button.
Windows | Shareware
Read More | Download Now
Business :: Inventory & Barcoding
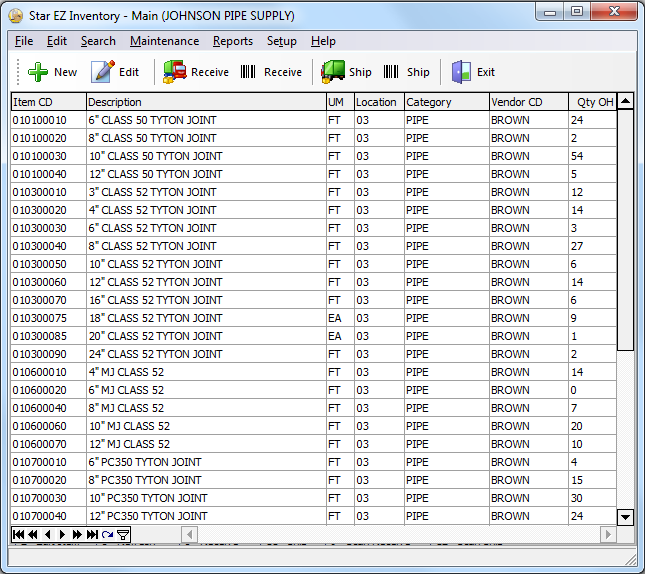 Star EZ Inventory is a simple yet powerful application program used to make the process of tracking and controlling your inventory fast and easy. There are many features that simplify the whole process of Tracking and Controlling Inventory. There is a fully functional database that stores your created Items, Vendors, and many more sets of data. Discover more info at www.starresoft.com
Star EZ Inventory is a simple yet powerful application program used to make the process of tracking and controlling your inventory fast and easy. There are many features that simplify the whole process of Tracking and Controlling Inventory. There is a fully functional database that stores your created Items, Vendors, and many more sets of data. Discover more info at www.starresoft.com
Windows | Shareware
Read More | Download Now


